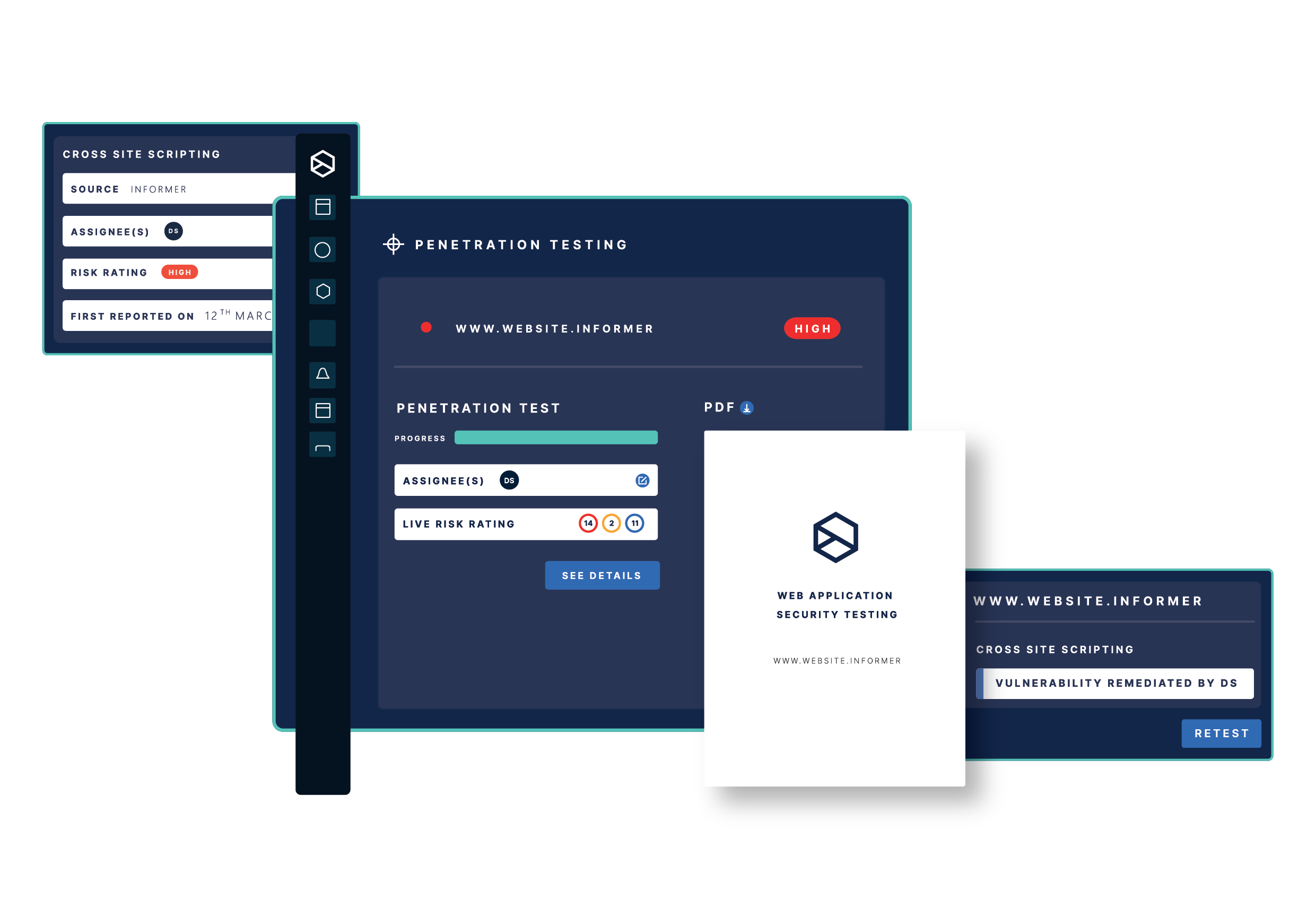
At Informer, we take a proactive approach to help organizations protect themselves from cyber threats by giving them a real-time view of their attack surface and live actionable vulnerability insights. Our attack surface management platform offers the unique benefits of combining live asset discovery, vulnerability scanning, and expert penetration testing in one platform to centralize vulnerability detection and remediation. Our experienced and highly skilled penetration testers, developers, and researchers collaborate extensively to offer business-critical security insights that empower you to fortify and scale your security program.
Brighton, United Kingdom
Founded in 2014
11-50 Employees
Working industry
IT, Software and Services, Cyber Security, Finance and Insurance
Type of company
Service provider
Locations
1 Headquarter
Number of services
1 Service
Specialised areas
Vulnerability Scanning, Penetration Testing, Attack Surface Management, Cybersecurity, Information Security, Web Application Scanner
informer.io offers a wide range of products and services
Service
Attack Surface Management Platform
Go to product >
An estimation about the ESG values based on digital data and signals. Important: The ESG scores are only based on information about the country, not the actual company itself
Country:
United Kingdom
Overall risk estimation:
Very low
The ESG Data of countries are based on public sources
Environment
A
Grade (A-E)
View details
Social
A
Grade (A-E)
View details
Governance
A
Grade (A-E)
View details
Get insights into the use cases of informer.io
Use case
Attack Surface Reduction
Financial Services, Software, Insurance, Retail
Attack surface reduction is crucial for modern organizations to minimize the risk of cyber attacks, protect sensitive data, and maintain a strong cybersecurity posture. Attack surface reduction involves identifying and reducing vulnerabilities and weaknesses that attackers can exploit to gain unauthorized access.
Use case
Asset Discovery and Inventory
Financial Services, Insurance, Software, Banking, Retail
Today’s external attack surfaces change constantly. New internet-facing assets regularly emerge and organizations struggle to keep up. Automated and continuous asset discovery and inventory equips IT and security teams with improved asset visibility helping avoid gaps with an up-to-date and accurate digital asset inventory.
informer.io operates in 1 country around the world
Get an overview of the locations of informer.io
Location
Country
State
City
Headquarter
United Kingdom
England
Brighton
Some frequent questions that have been asked about informer.io
Where is informer.io located?
The company headquarter of informer.io is located in Brighton, England, United Kingdom. It's worth noting, that the company may have more locations
How many employees does informer.io approximately have?
As of the latest available information informer.io has around 11-50 employees worldwide.
When was informer.io founded?
informer.io was founded in 2014
In which industries does informer.io mainly work?
The company informer.io has it's main focus in the industries of IT, Software and Services, Cyber Security, Finance and Insurance
Check out some interesting alternative companies to informer.io
NovaSec
Tel-Aviv, Israel
1-10 Employees
2018
We are a small group of security researchers who have mastered the way of modern web application penetration testing.With years of experience, and continuous learning, we strive to conduct one of the best web application pentests available.Most of us are also part-time bug bounty hunters.It allows us to keep continuously competing with other hackers from all around the world, and gives us the possibility to discover, and strengthen our weak spots, as there is always room for improvement.Automation plays a huge role in cyber security, as well as in web application penetration testing.Thanks to our years of experience in the field, we were able to develop advanced in-house tools that are capable of pulling bugs from any where at any time.They are not only capable of finding surface-layer vulnerabilities but also deeply hidden context-based security issues that previously required an immense amount of time, and experience to discover. We want to pursue this mission by developing highly advanced security vulnerability scanners that are not only blazing fast but also extremely reliable for any web application or API. We set precise goals that align with our mission. Built By The Same Penetration Testers That Helped Secure. Built-In Vulnerability Management Solution + Atlassian JIRA & GitHub Issues Integrated. Vulnerability scanning is a process where an automated program is looking for vulnerabilities and security misconfigurations in your web application or network.Usually, vulnerability scanners execute a predefined workflow to identify any exploitable vulnerability type.Once a vulnerability scanner has found and verified a valid security flaw, it creates an alert and reports the finding accordingly. However, the payload will unlikely work as the browser won't render the response as HTML.We solve this issue by validating every vulnerability found before notifying you (so you don't have to get excited and later realize that it was for nothing). Throughout our years of experience as web app penetration testers and bug bounty huntersWe sometimes used third-party vulnerability scanners to automate some of our workflows, and it didn't work out well for us.We had times when we found vulnerabilities while some vulnerability scanners just couldn't, even after pointing out where to scan.This never allowed us to put our trust in vulnerability scanners.
Intruder
London, United Kingdom
11-50 Employees
2015
Intruder was founded in 2015 to help solve the information overload crisis in vulnerability management. Intruder helps you do that, saving time on the easy stuff, so you can focus on the rest. Intruder gives you a real view of your attack surface combining continuous network monitoring, automated vulnerability scanning, and proactive threat response in one platform. Quite simply - the most important issues were often getting lost in the noise.Intruder's mission from day one has been to help divide the needles from the haystack, focusing on what matters, while ignoring the rest. Since its inception in 2015, Intruder has been awarded multiple accolades, was selected for GCHQ's Cyber Accelerator, and is now proud to have over 2,500 happy customers all over the world. With actionable results prioritized by context, Intruder helps you focus on fixing what matters, bringing an easy effectiveness to vulnerability management. Get actionable results prioritized by context so you can focus on the issues that matter.
Inspectiv
Los Angeles, United States
11-50 Employees
2018
Inspectiv's team of experts provide external validation of our security systems and help our team improve internal processes for dealing with threats and vulnerabilities. The Inspectiv platform streamlines our remediation process, and fixes are validated so we can feel confident our attack surface is secure. Delivered by cybersecurity experts following a methodical approach. We’re proud to help security professionals at leading organizations discover and manage impactful vulnerabilities before they’re exploited. A business-friendly bug bounty service without the complexity and cost from other providers.
Invaders Security
Dublin, Ireland
1-10 Employees
-
We provide comprehensive cybersecurity solutions that empower organizations to protect their valuable data, maintain operational continuity, and preserve the trust of their customers. Our vision is to create a world where businesses can thrive without fear of cyber threats. Our mission is to empower businesses by providing exceptional cybersecurity solutions that safeguard their digital assets, preserve their reputation, and ensure their continuity. We are committed to delivering innovative, tailored, and reliable services that stay one step ahead of evolving cyber threats. We provide a monthly, in-person update of emerging cyber security trends that is specifically designed for executive decision-makers like you. Invaders Threat Intelligence Vulnerability Management helps your Vulnerability Risk Analysts assess and prioritize security weak points. Invaders Cyber Shield is a comprehensive and practical training program designed to help small businesses build a strong defense system against cyber attacks. At Invaders, we are dedicated to protecting your digital assets from cyber threats.
SecIQ Technologies LLP
Bengaluru, India
11-50 Employees
2018
We are a team of industry experts with qualifications and experience ranging from CEH, CISSP, CSSLP, OSCP and CISA certifications and have enabled multiple start-ups to secure their products and infrastructure. We are one team; we will work as one. Our team is built of extremely skilled security professionals, subject matter experts, researchers and thought leaders with vast industry experience to provide you the best possible solutions to secure your organisation. As a deep-dive security testing provider, we uncover vulnerabilities which put your organization at risk, and provide guidance to mitigate them. We bring together the security research, proprietary technologies, and industry-leading security engineers to create the best penetration testing firm in the industry. So whether your focus is the external network, complex web applications, in the AWS cloud, IoT framework, Mobile Applications or social engineering testing, we have the specialists to fit your unique needs. To empower every person, product and organization on the internet to be secure. Create a community of security experts to secure customers from emerging security threats.
Fracture Labs
Sun Prairie, United States
1-10 Employees
2012
We are a small team of highly-skilled security experts with diverse backgrounds which makes us uniquely qualified for just about any project. Our offensive security experts may be hired to attack your systems and exploit your vulnerabilities, but we’re altruists at heart. Since then, the company has expanded and continued to focus on providing top-tier security assessments while relentlessly pursuing unbreakable systems in service to a more secure world of tech. The cornerstone of our business is helping organizations achieve their security goals as a trusted partner and that partnership means everything to us. Our intent is to deliver high-quality results for our clients and our team of security testers are hand-picked, elite infosec pros. Above all else, our experts were brought in for their technical skills, soft skills, high ethical standards, approach to continual learning, and passion for technology security. Our infosec experts can identify your weakest links so you can fix them before an attack. Our IoT security experts can expose critical security deficiencies in your embedded devices, before a hacker does.