
The B2B platform for the best purchasing descision. Identify and compare relevant B2B manufacturers, suppliers and retailers
Close
Filter
Result configuration
Continents
Select continent
Locations
Result types
Company type
Select company type
Industries
Select industry
Company status
Select company status preset
Number of employees
Min.
Max.
Founding year

北京微步在线科技有限公司
Dongcheng District, China
D
11-50 Employees
-
Key takeaway
ThreatBook is a leading provider of threat intelligence, offering a range of SaaS-based products and services that deliver comprehensive protection across cloud, traffic, and endpoints.
Reference
Product
Cyber Security Solutions_Security Operation | ThreatBook
ThreatBook
Dongcheng District, China
D
251-500 Employees
2015
Key takeaway
ThreatBook is a leading provider of threat intelligence, offering a range of SaaS-based products and services designed for comprehensive protection across cloud, traffic, and endpoints. Their focus on threat detection and response makes them a key player in the cybersecurity landscape.
Reference
Product
ThreatBook - Solutions
ThreatAgility
Huangpu District, China
D
1-10 Employees
2020
Key takeaway
ThreatAgility focuses on automotive cybersecurity, utilizing an AI-driven platform that enhances vehicle self-awareness and security. Their approach includes intelligent attack simulation to identify and prioritize cybersecurity requirements across vehicle systems.
Reference
Core business
Agile, Automotive Cybersecurity - ThreatAgility
Agile, intelligent cybersecurity, woven into the lifecycle of connected vehicles. ThreatAgility’s unique AI-driven platform enables self-aware, cybersecure vehicles.
Looking for more accurate results?
Find the right companies for free by entering your custom query!
25M+ companies
250M+ products
Free to use
Wynyard Group
Hong Kong Island, China
D
251-500 Employees
2011
Key takeaway
The Wynyard Group specializes in Cyber Threat Analytics, offering advanced technology solutions that enhance the capabilities of law enforcement agencies. Their Distributed SIEM solution aggregates and analyzes log data to identify suspicious activities, making it a valuable tool for threat intelligence.
Reference
Service
Distributed SIEM Solution | Cyber Threat Analytics | Wynyard Group
Distributed SIEM solution by Wynyard Group aggregates log data from the various connected devices and filters them for suspicious activity
CYPHER
Kowloon, China
D
1-10 Employees
-
Key takeaway
CYPHER is a cyber security consultancy that focuses on intelligence-based security assessments, offering services that simulate real-life hacking scenarios to identify vulnerabilities. Their tailored solutions make cyber security more accessible, particularly for SMEs.
Reference
Core business
Cypher | Security Testing, Security Consultant, Ethical Hacking
Infocean Technology
Kowloon, China
D
11-50 Employees
1999
Key takeaway
Infocean is dedicated to delivering specialized IT solutions, including security and threat vulnerability management. With a focus on risk assessments and advanced scanning technologies, Infocean helps organizations identify and address emerging security threats effectively.
Reference
Product
Threat/Vulnerability Management - Infocean Technology Co. Ltd.
Threat and Vulnerability Management Security threats facing organizations around the world are numerous and increasing daily. It is one of the most challenging and complex issues facing corporate IT today. By making use of advance scanning technologies, company is able to constantly discover new threat and
TEKID Limited
Changning District, China
D
11-50 Employees
2017
Key takeaway
TEKID emphasizes a holistic approach to Cyber Security, integrating expertise from various fields to enhance threat intelligence and digital safety. Their services include cyber-attack investigations, compliance projects, and active monitoring of digital assets, catering to the needs of both medium-sized and multinational organizations.
Reference
Core business
TEKID - Investigation & Discovery
Securing Businesses with Intelligence
CYBER.SO-Cyber Services HK
China
D
1-10 Employees
2020
Key takeaway
Cyber Services specializes in developing and implementing advanced cybersecurity measures, including threat intelligence. They utilize state-of-the-art tools to gather and process data on potential and emerging threats, ensuring the protection of their clients' confidential data and electronic assets.
Reference
Service
Services | CYBER.SO
Cyber Security Agency provides Cyber & Business intelligence, Cyber Security solutions, Investigations & Consultancy tailor made for each customer.
FuseClick
Hong Kong Island, China
D
11-50 Employees
2015
Key takeaway
FlashIntel is a leading Go-to-Market Intelligence Company that provides innovative tools like FlashInfo and FlashClick to help businesses optimize their sales and partnership processes. Their 'Social Intent' feature offers deep insights into prospects' needs, which is crucial for effective threat intelligence and understanding market dynamics.
Reference
Core business
FlashIntel - A leading Go-to-Market Intelligence Company
TD Intelligence Technology
Pudong, China
D
51-100 Employees
2016
Key takeaway
The company specializes in high-performance intelligence sensors and analytic tools that enhance traffic intelligence. This focus on providing robust traffic data can be integral to effective threat intelligence strategies.
Reference
Core business
About Us – TD Intelligence
Technologies which have been searched by others and may be interesting for you:
A selection of suitable products and services provided by verified companies according to your search.
Service
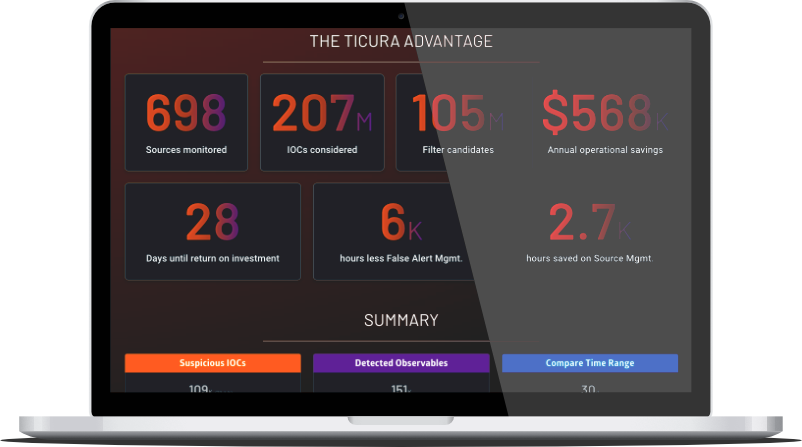
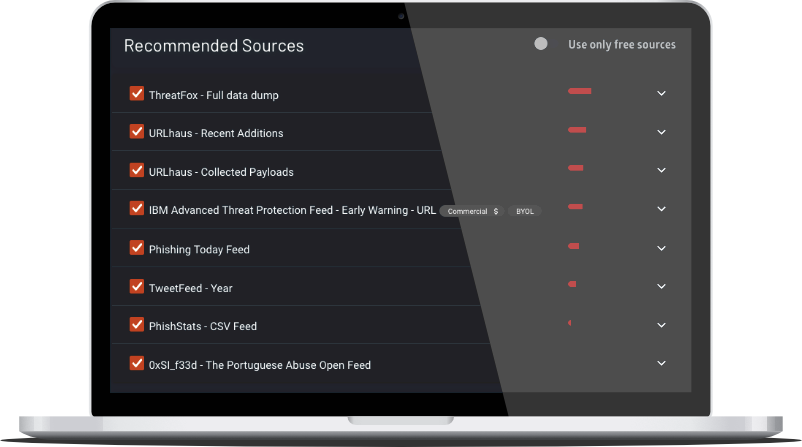
Source Recommendation Assessment
Go to product
A selection of suitable use cases for products or services provided by verified companies according to your search.
Use case
FInding the optimal Threat Intelligence
MSSP, Security
Ticura enriches existing threat intelligence programs with data from over 870 sources of network, public cloud, SaaS, endpoint and identity telemetry. Then, leveraging its proprietary detection engine, data science and machine learning, Ticura analyzes and surfaces the anomalies, incidents and threats to deliver optimal protection for your organization.
Use case
FInding the optimal Threat Intelligence
MSSP, Security
Ticura enriches existing threat intelligence programs with data from over 870 sources of network, public cloud, SaaS, endpoint and identity telemetry. Then, leveraging its proprietary detection engine, data science and machine learning, Ticura analyzes and surfaces the anomalies, incidents and threats to deliver optimal protection for your organization.
When exploring the Threat Intelligence industry in China, several key considerations emerge. First, regulatory frameworks are critical, as the Chinese government imposes strict data security and cybersecurity laws that affect how companies collect, analyze, and share threat intelligence. Understanding these regulations is essential for compliance and operational success. Challenges such as a rapidly evolving threat landscape and geopolitical tensions can complicate intelligence gathering and sharing. Additionally, the competitive landscape is marked by a mix of domestic firms and multinational corporations, each vying for market share in a growing field driven by increasing cyber threats. Opportunities abound, particularly in sectors like finance, healthcare, and critical infrastructure, where demand for robust threat intelligence solutions is escalating. Moreover, the global relevance of China's Threat Intelligence market cannot be overlooked, as its position in the global supply chain makes it a focal point for cyber threats. Environmental concerns related to data centers and their energy consumption are also becoming increasingly important, as companies aim for sustainability in their operations. Overall, a comprehensive understanding of these factors will greatly benefit those looking to navigate the complexities of the Threat Intelligence industry in China.
Some interesting numbers and facts about your company results for Threat Intelligence
| Country with most fitting companies | China |
| Amount of fitting manufacturers | 41 |
| Amount of suitable service providers | 40 |
| Average amount of employees | 11-50 |
| Oldest suiting company | 1999 |
| Youngest suiting company | 2020 |
Some interesting questions that has been asked about the results you have just received for Threat Intelligence
What are related technologies to Threat Intelligence?
Based on our calculations related technologies to Threat Intelligence are Big Data, E-Health, Retail Tech, Artificial Intelligence & Machine Learning, E-Commerce
Which industries are mostly working on Threat Intelligence?
The most represented industries which are working in Threat Intelligence are IT, Software and Services, Other, Defense, Electronics and Electrical engineering, Finance and Insurance
How does ensun find these Threat Intelligence Companies?
ensun uses an advanced search and ranking system capable of sifting through millions of companies and hundreds of millions of products and services to identify suitable matches. This is achieved by leveraging cutting-edge technologies, including Artificial Intelligence.