
The B2B platform for the best purchasing descision. Identify and compare relevant B2B manufacturers, suppliers and retailers
Close
Filter
Result configuration
Continents
Select continent
Locations
Result types
Company type
Select company type
Industries
Select industry
Company status
Select company status preset
Number of employees
Min.
Max.
Founding year
Zentera Systems
San Jose, United States
B
11-50 Employees
2012
Key takeaway
Zentera Systems, Inc. emphasizes the importance of a Zero Trust approach, highlighting their CoIP Platform that ensures all network access is authorized, thereby enhancing security without hindering productivity. Their solutions are designed to help businesses, regardless of size, effectively implement Zero Trust security, even for legacy applications and data.
Reference
Product
Zero Trust Security | Zentera Systems, Inc.
The CoIP overlay provides an instant on-ramp for Zero Trust, enabling companies to adopt a Zero Trust security posture for even legacy apps and data.
Riverside Research
Lexington, United States
B
501-1000 Employees
1967
Key takeaway
Riverside Research emphasizes its commitment to delivering innovative solutions for national security challenges, which aligns with the principles of Zero Trust by focusing on independent, trusted expertise and collaboration. Their mission to provide timely and cost-effective solutions may be relevant for organizations looking to implement Zero Trust strategies.
Reference
Service
Zero Trust
Trustgrid
Austin, United States
B
11-50 Employees
2016
Key takeaway
The Trustgrid platform incorporates zero trust remote user access (ZTNA) as part of its innovative networking and edge computing solutions. This approach enhances connectivity and application delivery across various environments, making it particularly relevant for managing secure connections in fintech applications.
Reference
Core business
Zero Trust Network Access Explained - trustgrid.io
VM Blog | Article
Looking for more accurate results?
Find the right companies for free by entering your custom query!
25M+ companies
250M+ products
Free to use
Ascent Solutions
Minneapolis, United States
B
101-250 Employees
2008
Key takeaway
The company emphasizes its commitment to cybersecurity, highlighting its partnership with experts dedicated to protecting organizations through essential plans and programs. This aligns with the principles of Zero Trust, which focuses on rigorous security measures to defend against evolving threats.
Reference
Product
Zero Trust
Ridge IT
Richmond, United States
B
1-10 Employees
-
Key takeaway
Ridge IT is a leading cybersecurity firm that emphasizes Zero Trust principles in its approach. They provide tailored cybersecurity solutions and managed services, ensuring comprehensive protection for clients across various sectors.
Reference
Product
Zero Trust – Ridge IT
Stygian Vortex Security Consultants
United States
B
1-10 Employees
2021
Key takeaway
Keith Glynn, with his extensive experience in enterprise security architecture and specialized knowledge in operational technology and IoT security, is well-equipped to assist manufacturers in implementing and operationalizing Zero Trust principles. His expertise in creating cybersecurity ecosystems helps protect supply chains from cyber-attacks, making him a valuable asset in the transition to a Zero Trust model.
Reference
Service
Zero Trust Implementation & Operationalization – Stygian Vortex Security Consultants
ModernCyber
Melbourne, United States
B
1-10 Employees
2021
Key takeaway
ModernCyber emphasizes the importance of zero trust principles, such as least privilege and system integration, as critical factors in enhancing cybersecurity and preventing breaches. Their innovative services and expertise aim to provide organizations with scalable access control solutions that align with zero trust strategies.
Reference
Service
Zero Trust as a Service (ZTaaS) | ModernCyber
Zero Trust by Default
Gradient
Boston, United States
B
11-50 Employees
2018
Key takeaway
Gradient Cybersecurity Mesh (GCM) is a comprehensive zero-trust solution that integrates hardware-based roots of trust with advanced software to effectively eliminate credential-based cyberattacks. By continuously monitoring device identity and integrity, GCM ensures secure credential issuance and policy management, providing robust protection for enterprise environments.
Reference
Product
Gradient Technologies - Enterprise Zero Trust Access
Hillstone Networks
Sunnyvale, United States
B
501-1000 Employees
2006
Key takeaway
Hillstone Networks offers a comprehensive Zero Trust security architecture through its ZTNA Solution, which enhances protection and visibility into user and device behavior across various locations. This approach ensures secure access from any device, adapting to infrastructure changes while safeguarding applications and data.
Reference
Product
Zero Trust Network Access (ZTNA) Solutions | Hillstone Networks
Hillstone ZTNA supports a wide range of authentication schemes, popular enterprise devices, and operating systems.
Datalink
Chanhassen, United States
B
501-1000 Employees
1958
Key takeaway
The company emphasizes its commitment to addressing top security concerns, including evolving cyberthreats, through innovative solutions. Their offerings include a Zero Trust Assessment, which is integral to modern security strategies.
Reference
Service
Zero Trust Assessment
Technologies which have been searched by others and may be interesting for you:
A selection of suitable products and services provided by verified companies according to your search.
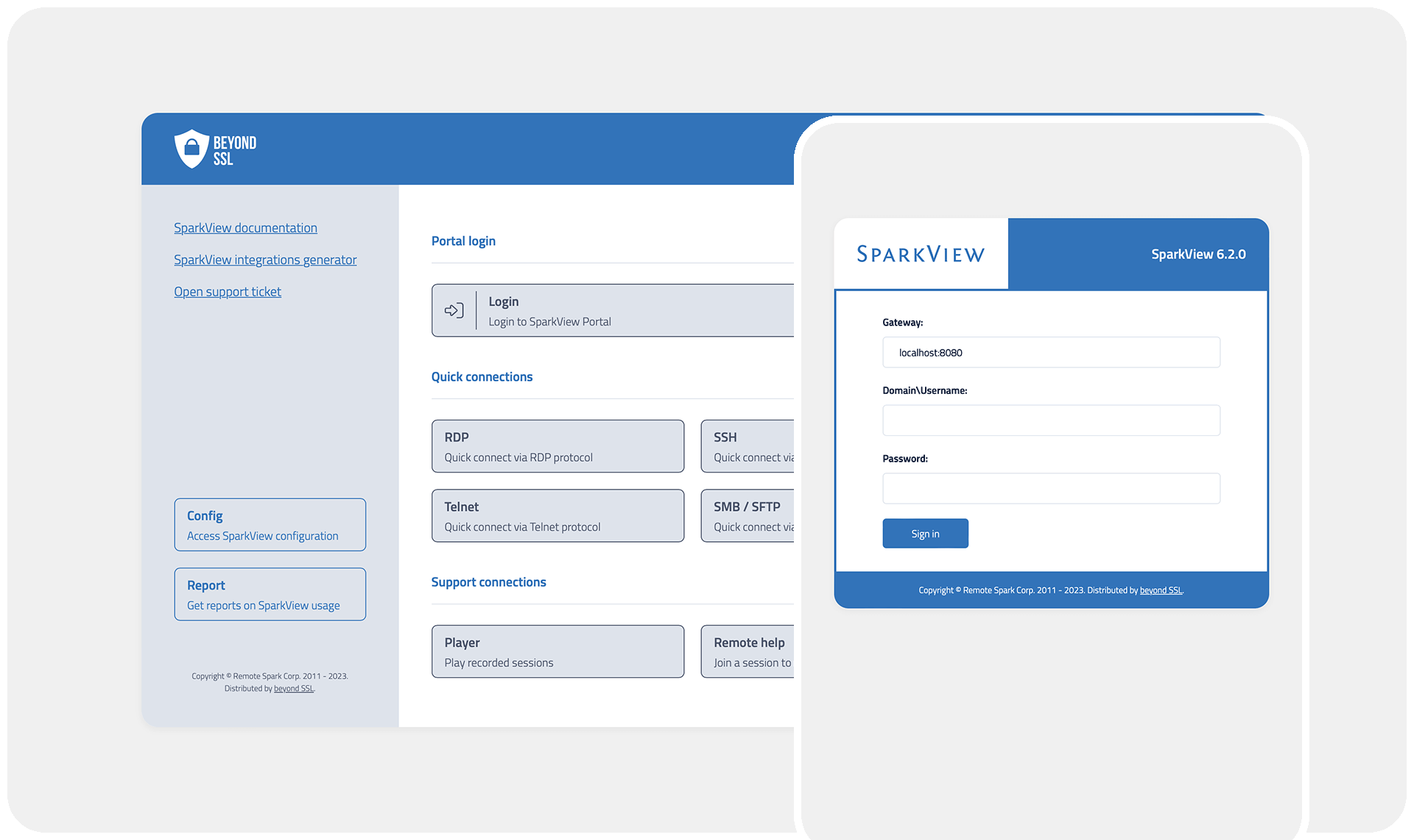
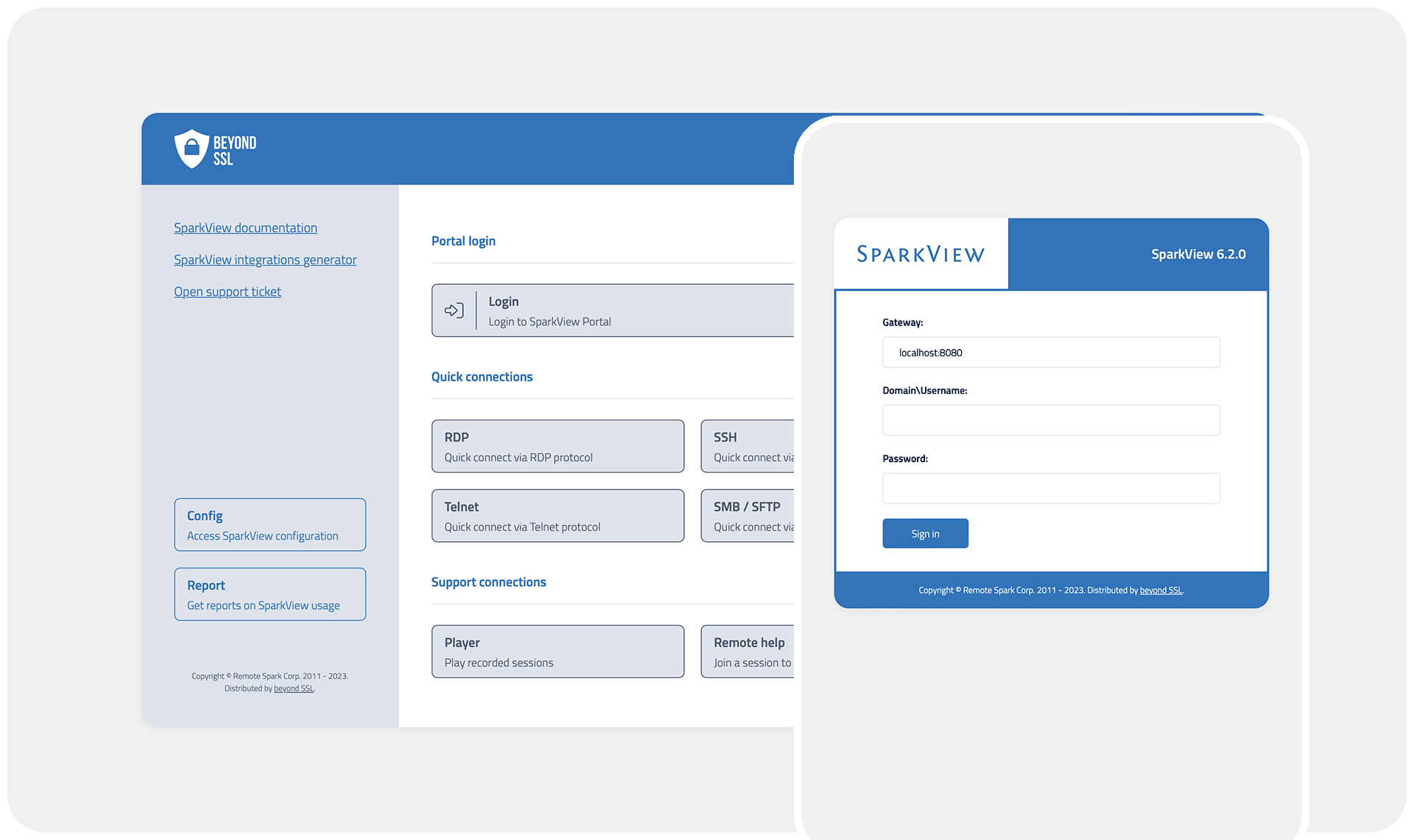
Product
SparkView ZTNA
Go to product
A selection of suitable use cases for products or services provided by verified companies according to your search.

Use case
Access any app on your Chromebook—even if it's not ChromeOS-native
Education, Gov, All Industries
SparkView lets you get even more out of your Chromebooks! SparkView is easy to use via the browser or as an app (PWA) and gives your Chromebook superpowers: you get secure and fast access to internal company apps, desktops, and servers directly in your browser. With SparkView, you can also seamlessly access non-ChromeOS-native apps—whether they’re specially developed applications, legacy systems, Windows apps, macOS apps, and more—ensuring you have the right tools at your fingertips, no matter the platform. And best of all: no data leaves the company!
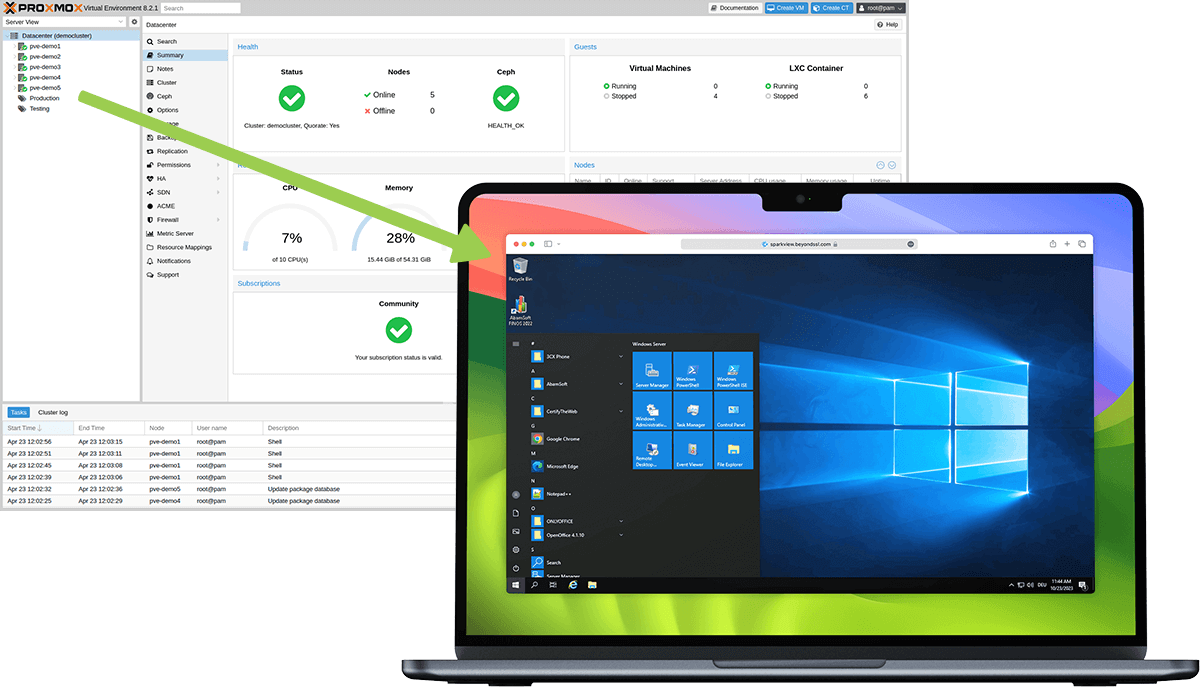
Use case
Secure Remote Access to Your Virtualization Environment with Proxmox
all
The Perfect Combination: SparkView and Proxmox for Secure and Efficient IT Infrastructures. With Zero Trust and virtualization, you can eliminate VPN security risks, reduce administrative complexity, and minimize the cost pressures of traditional solutions. Maximum security through Zero Trust > SparkView grants access to Proxmox resources only after strict authentication. >Each access package is checked individually, which prevents lateral movement. Simple administration >Proxmox offers centralized management for VMs and containers. >SparkView enables administrators to easily control access rights for Proxmox services - without separate client software. Cost efficiency >Proxmox and SparkView offer excellent value. >No need for expensive VPN licenses or additional hardware.
Use case
Clientless ZTNA-compliant Remote Access - without VPN
all
Traditional VPNs are no longer sufficient for securing remote access. SparkView offers a clientless Zero Trust Network Access (ZTNA) solution, enabling secure, browser-based access to internal applications and desktops—without the complexity of VPNs. Users can connect seamlessly from any device while organizations maintain granular access control and zero trust security principles, ensuring that only authorized users gain entry to corporate resources. SparkView enhances security, flexibility, and user experience, making remote work efficient and risk-free.

Use case
Access any app on your Chromebook—even if it's not ChromeOS-native
Education, Gov, All Industries
SparkView lets you get even more out of your Chromebooks! SparkView is easy to use via the browser or as an app (PWA) and gives your Chromebook superpowers: you get secure and fast access to internal company apps, desktops, and servers directly in your browser. With SparkView, you can also seamlessly access non-ChromeOS-native apps—whether they’re specially developed applications, legacy systems, Windows apps, macOS apps, and more—ensuring you have the right tools at your fingertips, no matter the platform. And best of all: no data leaves the company!
When exploring the Zero Trust industry in the United States, several key considerations come into play. A fundamental aspect is understanding the regulatory landscape, including compliance with standards such as the Federal Risk and Authorization Management Program (FedRAMP) and the Cybersecurity Framework established by NIST. Organizations must also be aware of the challenges related to implementation, such as integrating existing systems and managing user access without compromising security. Opportunities abound in the growing demand for Zero Trust solutions, driven by increasing cyber threats and the shift to remote work models. Companies that prioritize robust identity and access management, extensive monitoring capabilities, and data protection strategies are likely to thrive. Additionally, the competitive landscape is rapidly evolving, with both established tech giants and innovative startups vying for market share, emphasizing the importance of staying informed about industry trends and emerging technologies. Environmental concerns are also gaining attention, particularly regarding energy-efficient data centers and sustainable practices in software development. The Zero Trust model's global relevance is significant, as organizations worldwide are adopting these principles to enhance their security posture. As such, potential investors and stakeholders should carefully evaluate these factors to make informed decisions in the Zero Trust market.
Some interesting numbers and facts about your company results for Zero Trust
| Country with most fitting companies | United States |
| Amount of fitting manufacturers | 3020 |
| Amount of suitable service providers | 3167 |
| Average amount of employees | 11-50 |
| Oldest suiting company | 1958 |
| Youngest suiting company | 2021 |
Some interesting questions that has been asked about the results you have just received for Zero Trust
What are related technologies to Zero Trust?
Based on our calculations related technologies to Zero Trust are Big Data, E-Health, Retail Tech, Artificial Intelligence & Machine Learning, E-Commerce
Who are Start-Ups in the field of Zero Trust?
Start-Ups who are working in Zero Trust are Stygian Vortex Security Consultants, ModernCyber
Which industries are mostly working on Zero Trust?
The most represented industries which are working in Zero Trust are IT, Software and Services, Other, Defense, Telecommunications, Finance and Insurance
How does ensun find these Zero Trust Companies?
ensun uses an advanced search and ranking system capable of sifting through millions of companies and hundreds of millions of products and services to identify suitable matches. This is achieved by leveraging cutting-edge technologies, including Artificial Intelligence.